roccomarcy
Members-
Gesamte Inhalte
239 -
Registriert seit
-
Letzter Besuch
Profile Fields
-
Member Title
Newbie
Letzte Besucher des Profils
Der "Letzte Profil-Besucher"-Block ist deaktiviert und wird anderen Benutzern nicht angezeit.
Fortschritt von roccomarcy
-
autom. Sicherung und Wiederherstellung einer Datenbank
roccomarcy antwortete auf ein Thema von roccomarcy in: MS SQL Server Forum
selbes System, sogar selbe Instanz. Nur anderer Name der Datenbank. -
roccomarcy folgt jetzt dem Inhalt: Active-Directory / LDAP Proxy , autom. Sicherung und Wiederherstellung einer Datenbank , Windows 11 24H2 / Fehler 5719 aber keine Einschränkungen? und 4 Weitere
-
autom. Sicherung und Wiederherstellung einer Datenbank
roccomarcy hat einem Thema erstellt in: MS SQL Server Forum
Guten Morgen, ich würde gerne in definierten Intervallen eine Datenbank sichern und unter anderem Namen wiederherstellen. Dies passiert heute schon manuell, der Vorgang soll allerdings automatisiert werden. Es geht dabei um die Bereitstellung von Produktivdaten in einem Testsystem. Gibt es dafür Boardmittel oder hat das schon jemand via Skript gebaut? -
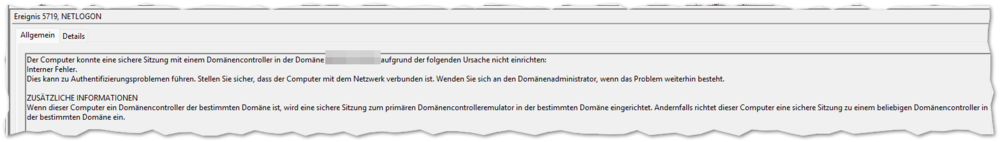
Windows 11 24H2 / Fehler 5719 aber keine Einschränkungen?
roccomarcy antwortete auf ein Thema von roccomarcy in: Windows 11 Forum
Wir haben mit der Konfiguration MaxOfflineTimeLimit für den Dienst Netlogon herumexperimentiert und auch via GPO konfiguriert, dass auf das Netzwerk gewartet werden soll. Die Startzeit verlängert sich minimal vom System, aber der Fehler wird weiterhin protokolliert. -
Windows 11 24H2 / Fehler 5719 aber keine Einschränkungen?
roccomarcy hat einem Thema erstellt in: Windows 11 Forum
Hallo zusammen, wir vernehmen auf diversen Windows 11 24H2-Systemen, die entweder frisch(!) installiert oder via Inplace-Upgrade aktualisiert wurden, den Fehler NETLOGON 5719 auf. Allerdings konnten keine Einschränkungen (Zugriff Freigaben, freigegebene Drucker, RDP-Zugriff auf Terminalserver, usw) festgestellt werden. Konnte jemand schon ähnliches feststellen und hat ggf. eine Lösung dafür parat? Ein Netlogon.log habe ich bereits erstellt. Ausschnitt daraus mit Schwärzungen: 07/16 10:01:36 [CRITICAL] [5976] C:\WINDOWS\system32\config\dclocadminmappings.log: Unable to open. 2 07/16 10:01:36 [CRITICAL] [5976] C:\WINDOWS\system32\config\dclocscanmappings.log: Unable to open. 2 [...] 07/16 10:01:36 [CRITICAL] [5976] C:\WINDOWS\system32\config\netlogon.ftj: Unable to open. 2 07/16 10:01:36 [INIT] [5976] Getting cached trusted domain list from binary file. [...] 07/16 10:01:36 [CRITICAL] [5976] NlCacheJoinDomainControllerInfo: Failed to open JoinDomain breadcrumb in registry; assuming 07/16 10:01:36 [CRITICAL] [5976] NlCacheJoinDomainControllerInfo: therefore that this is not a post-join scenario. 07/16 10:01:36 [CRITICAL] [5976] NetpDcGetName: NlCacheJoinDomainControllerInfo returned success [...] 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSessionSetup: Denied access as we could not authenticate with Kerberos 0xC002002E 07/16 10:01:37 [CRITICAL] [5976] Assertion failed: ClientSession->CsState == CS_IDLE (Source File: onecore\ds\netapi\svcdlls\logonsrv\server\lsrvutil.c, line 3981) 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSessionSetup: Denied access as we could not authenticate with Kerberos (translated status) 0xC00000E5 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSetStatusClientSession: Set connection status to c00000e5 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSetStatusClientSession: Unbind from server \\test1-dc01.TEST-dom.local (TCP) 0. 07/16 10:01:37 [MISC] [5976] Eventlog: 5719 (1) "TEST-DOM" 0xc00000e5 3dc54378 84808124 847d677c e2aadc59 xC.=$...|g}.Y... 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSetStatusClientSession: Set connection status to c000005e 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSessionSetup: Session setup Failed 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSessionSetup: Try Session setup 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlDiscoverDc: Start Synchronous Discovery 07/16 10:01:37 [MISC] [5976] NetpDcInitializeContext: DSGETDC_VALID_FLAGS is c3fffff1 07/16 10:01:37 [MAILSLOT] [5976] NetpDcPingListIp: TEST-dom.local.: Sending UDP ping to 10.1.0.100 07/16 10:01:37 [ERROR] [1608] NlpGenerateIumBoundMachineAuthCert: Provisioning interface not responding; treating as if IUM weren't available: 1717 07/16 10:01:37 [MISC] [1608] NlpStoreKeyInDS: IUM Provisioning interface not up. 07/16 10:01:37 [ERROR] [1608] NlpStoreKeyInDS: No machine bound certificate could be created: 1717 07/16 10:01:37 [ERROR] [1608] NlProvisionMachineAuthKey: Unable to store auth key in DS: 1717 07/16 10:01:37 [MISC] [5976] NetpDcAllocateCacheEntry: new entry 0x0000023BF11CC7D0 -> DC:test1-DC01 DnsDomName:TEST-dom.local Flags:0x3f1fc 07/16 10:01:37 [MISC] [5976] NetpDcGetName: NetpDcGetNameIp for TEST-dom.local. returned 0 07/16 10:01:37 [MISC] [5976] NetpDcDerefCacheEntry: destroying entry 0x0000023BF1673240 07/16 10:01:37 [MISC] [5976] LoadBalanceDebug (Flags: FORCE DSP AVOIDSELF ): DC=test1-DC01, SrvCount=1, FailedAQueryCount=0, DcsPinged=1, LoopIndex=0 07/16 10:01:37 [PERF] [5976] NlSetServerClientSession: Not changing connection (0000023BF16B9168): "\\test1-dc01.TEST-dom.local" ClientSession: 0000023BF1672530TEST-DOM: NlDiscoverDc: Found DC \\test1-dc01.TEST-dom.local 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSessionSetup: Negotiated flags with server are 0x612fffff 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSetStatusClientSession: Set connection status to 0 07/16 10:01:37 [DOMAIN] [5976] Setting LSA NetbiosDomain: TEST-DOM DnsDomain: TEST-dom.local. DnsTree: TEST-dom.local. DomainGuid:a218299c-ed14-47f8-9397-f8f4b3d48e24 07/16 10:01:37 [LOGON] [5976] NlSetForestTrustList: New trusted domain list: 07/16 10:01:37 [LOGON] [5976] 0: TEST-DOM TEST-dom.local (NT 5) (Forest Tree Root) (Primary Domain) (Native) 07/16 10:01:37 [LOGON] [5976] Dom Guid: a218299c-ed14-47f8-9397-f8f4b3d48e24 07/16 10:01:37 [LOGON] [5976] Dom Sid: S-1-5-21-1659004503-1935655697-1343024091 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSetStatusClientSession: Set connection status to 0 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSessionSetup: negotiated 612fffff flags rather than 0 07/16 10:01:37 [SESSION] [5976] TEST-DOM: NlSessionSetup: Session setup Succeeded 07/16 10:01:37 [INIT] [5976] Started successfully ach, kurzer Nachtrag: Als Fehlermeldung wird "Interner Fehler." ausgegeben in der Ereignisanzeige. -
mstsc / Remote Desktop funktioniert sporadisch nicht
roccomarcy hat einem Thema erstellt in: Windows 11 Forum
Hallo zusammen, ich kämpfe seit einiger Zeit mit dem Problem, dass bei vereinzelten Anwendern die Remote Desktop Verbindung bzw. Anwendung mstsc nicht funktioniert. Der Anwender öffnet via RemoteApp verschiedene Anwendungen auf dem Serversystem. Die Umgebung ist wie folgt: Client: Windows 11 24H2 mit akt. Juni 2025 Updates Server: Windows Server 2016 DataCenter (kein Broker, direkt) Es kommt sporadisch dazu, dass bei Klick auf die rdp-Verbindung der Prozess im Hintergrund (Task-Manager, mstsc.exe) startet, aber die Anwendung sich nicht öffnet. Wenn man den Prozess killt, funktioniert es in 50% der Fälle, in den anderen 50% allerdings nicht. Häufig ist es auch so, dass dem Anwender die Sitzung getrennt wird und er will diese wieder mit aufnehmen und die Verbindung kann nicht hergestellt werden. Workaround ist das Abmelden des Benutzers auf dem Terminalserver. Habt Ihr eine Idee, wo ich ggf. tiefer forschen könnte um dem Problem her zu werden? -
Powershell - Prozesse inkl. Benutzernamen als normaler Benutzer auslesen
roccomarcy hat einem Thema erstellt in: Windows Forum — Scripting
Hey, wir überwachen unsere Systeme via Icinga2 und dem dazugehörigen Powershell-Framework für die Windows-Systeme. Ich habe nun ein Skript geschrieben, welches auf dem zu überwachenden Server liegt und durch den Icinga2-Agent gestartet wird. Dieses Skript soll prüfen, ob ein bestimmter Prozess unter einem bestimmten Benutzer gestartet wurde. Kommen wir jetzt zu dem Problem: Wenn ich das Skript als Administrator ausführe funktioniert es ohne Schwierigkeit, sobald das Skript aber unter dem Benutzerkontext des Icinga2-Agent (normales Benutzerkonto) ausgeführt wird, dann gibt es keine Rückmeldung bzgl. dem Benutzernamen. Ich habe dann schon die WMI-Konfiguration angepasst und dem Benutzer mehr Rechte eingeräumt, leider ohne Erfolg. Meine Frage wäre daher: Hatte schon jemand ähnliches Thema und dafür eine elegante Lösung gefunden? Ich kann den Icinga2-Agent natürlich in die Gruppe der lokalen Administratoren verschieben, aber das ist eigentlich nicht der richtige Weg (mMn). -
Windows 11 24H2 / Zugriff via RDP nicht möglich?
roccomarcy antwortete auf ein Thema von roccomarcy in: Windows 11 Forum
Guten Morgen zusammen, nach Installation vom aktuellen CU (November) für die VM, war RDP wieder problemlos möglich. Gruß -
Windows 11 24H2 / Zugriff via RDP nicht möglich?
roccomarcy hat einem Thema erstellt in: Windows 11 Forum
Hallo zusammen, ich habe Windows 11 Pro 24H2 frisch als VM installiert und in mein Active-Directory eingebunden. Alle Updates wurden bereitgestellt und ich habe RDP aktiviert sowie in der Firewall freigegeben. Wenn ich jetzt versuche eine Verbindung zu dieser VM von einem Windows 10 oder Windows 11 Rechner herzustellen, wird diese abgewiesen. Ich habe die Firewall auf beiden Systemen auch schon deaktiviert, leider ohne Besserung. Ist jemanden von euch das Verhalten unter Windows 11 bekannt? Bei einer Installation, die ich via Inplace-Upgrade auf Windows 11 aktualisiert habe, tritt dieses Verhalten nicht auf. -
pingcastle - Ergebnisse umsetzen
roccomarcy antwortete auf ein Thema von roccomarcy in: Windows Forum — Security
Guten Morgen, ich würde das Thema gerne noch mit einer Rückmeldung von meiner Seite abschließen. Die angesprochenen Punkte aus meinem Eingangspost und noch etwas mehr habe ich als Dienstleistung mit/bei Norbert eingekauft und wurden von uns gemeinsam umgesetzt. Dies soll jetzt keine Werbung für Norbert oder seinem Arbeitgeber sein, ich kann allerdings dennoch mal einen Dank aussprechen, dass die gesamte Umsetzung reibungslos und ohne Ausfall/Störung des laufenden Betrieb erfolgt ist. Das wird nun niemanden weiterhelfen, der in Zukunft vor ähnlichen Problemen stehen wird und bricht natürlich etwas die Idee eines Forums. Aber bei den Brocken an Themen kann ich eigentlich nur dazu raten einen Dienstleister aufzusuchen, der sein Handwerk versteht. Schont am Ende auf allen Seiten die Nerven und auch den Geldbeutel. Gruß -
Guten Morgen zusammen, wir mussten auf diversen Systemen feststellen, dass der Speicherplatz auf den Arbeitsplätzen zu Neige geht. Abhilfe schafft die Bereinigung via Datenträgerbereinigung. Da ich nun keine Lust habe dieses auf den ganzen Maschinen manuell durchzuführen, wäre meine Frage, ob folgender Weg sinnvoll ist? => Profil via /sageset erstellen. => Registry-Einstellungen exportieren. => Batch mit Registry-Einstellungen sowie cleanmgr-Ausführung erstellen. => Batch via Aufgabenplanung regelmäßig ausführen lassen (Verteilung via Gruppenrichtlinie) Für (bessere) Vorschläge bin ich offen ..
-
Hallo, folgende Anforderung hat jetzt nur bedingt was mit Active-Directory zu tun, aber ich habe die Hoffnung, das jemanden so ein Szenario schon einmal vor dir Füße gefallen ist. Ich habe eine Anwendung, in dieser Anwendung kann ich Benutzer hinterlegen und in der Benutzerkonfiguration sagen, dass dieser Benutzer sich mit einem AD/LDAP-Server authentifizieren soll. Das haben wir bereits durchgeführt für DomäneA. Jetzt kommen wir zum spannenden Teil - nun sollen in der Anwendung Benutzer aus DomäneB aufgenommen werden, die Anwendung lässt aber nur die Konfiguration eines LDAP-Servers für alle Benutzer zu. Mein Gedanke wäre nun eine Art LDAP-Proxy in der Anwendung zu hinterlegen. Auf diesem Proxy wird dann konfiguriert, wenn die Anmeldung für BenutzerDomäneA kommt, geht es an die DCs von DomäneA. Bei BenutzerDomäneB natürlich an BenutzerDomäneB. Vielen Dank vorab und ein schönes Wochenende.
-
pingcastle - Ergebnisse umsetzen
roccomarcy antwortete auf ein Thema von roccomarcy in: Windows Forum — Security
Guten Morgen zusammen, ich habe mit NorbertFe auf anderer Ebene Kontakt aufgenommen, um die Probleme außerhalb des Forum zu lösen. Ergebnisse kann ich nachgelagert in den Thread packen, solang von Norbert nichts dagegen spricht. Den Einwand von cj_berlin habe ich berücksichtigt und mir/uns für kommende Veranstaltung im Juli einen Slot reserviert. Ich denke in der Kombination werden sich die Themen gut lösen lassen und auch das Wissen Inhouse stärken. Gruß -
pingcastle - Ergebnisse umsetzen
roccomarcy antwortete auf ein Thema von roccomarcy in: Windows Forum — Security
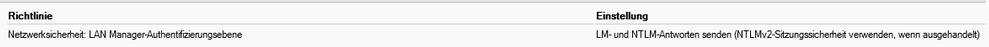
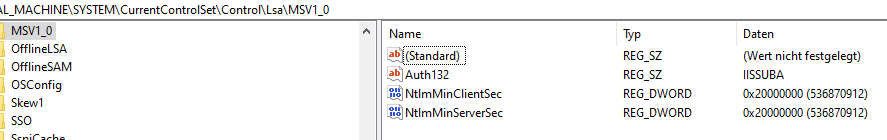
Okay, grad nochmal geschaut - tatsächlich steht der Wert auf 1. Das heißt für mich erstmal oben genannte LAN Manager Auth anpassen und danach Extended Protection konfigurieren, right? -
pingcastle - Ergebnisse umsetzen
roccomarcy antwortete auf ein Thema von roccomarcy in: Windows Forum — Security
Ja, das hast du gesagt. Aber was bedeutet das im Detail? Ich hatte ja einen Auszug aus der GPO oben gepostet und einen Screenshot aus der Registry. Bin ich damit auf der 'sicheren' Seite für EP? Oder lauf ich damit auf ein Problem? Laut GPO ist NTLM v2 ja aktiv, wenn ausgehandelt? -
pingcastle - Ergebnisse umsetzen
roccomarcy antwortete auf ein Thema von roccomarcy in: Windows Forum — Security
Moin, ich hab mir das mal etwas angeschaut - muss auf jeden Fall auf meinem Exchange TLS 1.2 via Skript aktivieren. Bin dann über div. Beiträge bei Microsoft darüber gestolpert, dass das bei den Clients auch aktiv sein muss. Das sollte es aber ja eh per se - oder muss ich hier auch was vorbereiten? Wenn ich die üblichen PS-Skripts abfeuere, dann kommt aus der Registry auf dem Client nichts zurück. Kann ich das irgendwo valide prüfen? Und es wird wohl NTLM v2 vorrausgesetzt. Ich habe via Gruppenrichtlinie ja noch folgendes konfiguriert. Laut Registry wird am Client auch NTLM v2 verwendet.